Behavioral Visibility: Moving Beyond Activity to Understand Engagement, Sentiment, and Intent
Behavioral visibility helps organizations move beyond activity data to understand engagement, sentiment, and intent. By adding context to workforce behavior, teams can detect insider risk earlier, reduce false positives, and make more informed decisions. read more
Browse by category
Select a category to see more related content
Why Boards Must Take the Lead on Insider Risk Oversight
Key Takeaways Insider Risk Is Business Risk Insider threats have swiftly become one of the most prevalent and financially burdensome forms of cyber risk. This necessitates immediate board-level visibility ... read more
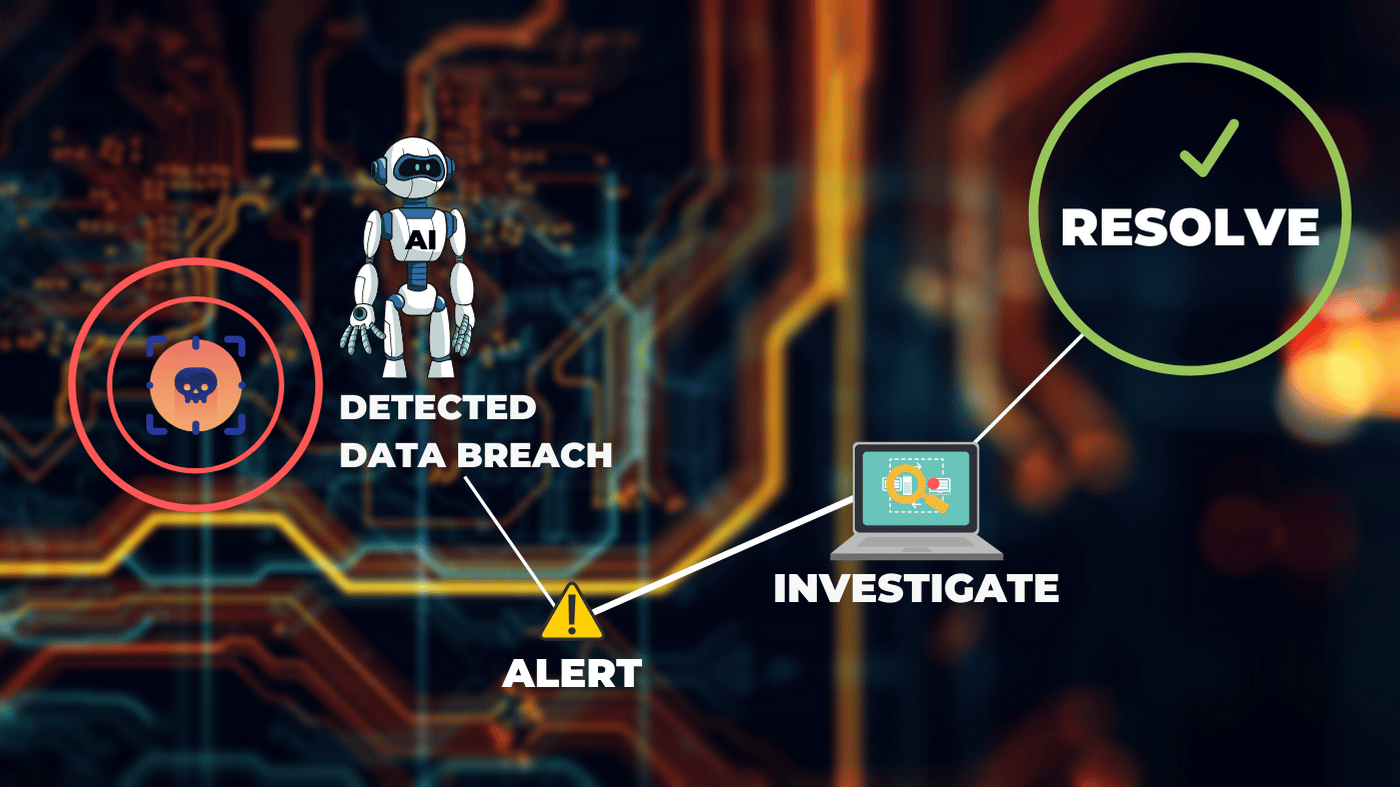
Predict and Prevent: How AI is Changing Insider Risk Management
Key Takeaways Insider risk is now a board-level concern 83% of organizations experienced an insider-related incident in 2024, making it one of the most pervasive cybersecurity challenges today. (IBM, Insider ... read more
Beyond Productivity – Using UAM to Understand Team Capacity & Burnout Risk
Burnout-related disengagement can cost organizations up to $21,000 per employee annually, or $5 million for a 1,000-person company. High workloads, digital fatigue, and constant multitasking are typical in modern workplaces. Many organizations struggle to recognize these signs early enough to act. Every day saved through proactive intervention helps recoup a portion of the $ 4,000–$ 21,000 per employee burnout risk. read more
Beyond the Perimeter: Rethinking Security from the Inside Out
Key Takeaways Insider Threats Are a Boardroom Issue, Not Just an IT Problem With rising accountability for compliance and resilience, CISOs must own internal risk visibility as part of their strategic ... read more
Redefining Accountability: How User Activity Monitoring Supports Remote Workforce Management
Key Takeaways Stop guessing and start guiding. UAM provides the visibility to act early and lead with confidence. Accountability that motivates. Use real insights to empower employees, not punish ... read more
Who Buys Insider Risk Management? A Business Case Across Roles
Key Takeaways: Insider Threats Are a Business Risk, Not Just a Security Concern Seventy-four percent of cybersecurity incidents originate from within the organization. Insider Risk Management (IRM) ... read more
Securing Your SaaS Future: How Veriato User Activity Monitoring (UAM) Addresses Key SaaS Challenges
Key Takeaways: Veriato UAM enhances IP protection with real-time activity monitoring. UAM identifies and mitigates risks from employee moonlighting. Productivity and accountability among remote ... read more
Protecting Client Data: How User Activity Monitoring (UAM) Supports Compliance in Financial Services
Key Takeaways: UAM supports—but does not replace—regulatory compliance. It provides compliance, HR, and legal teams with detailed user activity logs that help demonstrate the enforcement of internal ... read more
Infographic: Seeing is Securing: The Critical Need for Visibility in Insider Risk Management
Discover how Veriato's Seeing is Securing approach empowers businesses with advanced user activity monitoring. This infographic highlights how real-time visibility, behavioral analytics, and risk scoring help detect insider threats, boost productivity, and ensure compliance. See the full picture—because what you can’t see, you can’t secure. read more
Seeing is Securing: Why Insider Threats Could Be Your Company’s Biggest Blind Spot
Insider threats are on the rise. Learn how real-time monitoring and Insider Risk Management (IRM) can help protect your data, reputation, and operations. read more
The Power of Data: The Foundation of Better Workforce Insights
Discover how comprehensive data collection empowers better workforce management, enhanced security, and simplified compliance. Learn how Veriato UAM provides actionable insights to foster a secure, engaged, and productive workplace. read more
Why User Activity Monitoring (UAM) is a Must for SMBs
SMBs see the value of user activity monitoring in gaining deep insights for more intelligent decisions, so they trust Veriato's innovative management system. read more
Smart Year-End IT Investments- A Trifecta for ROI
As the year wraps up, many IT, security, compliance, and HR teams have unspent budgets that won't roll over. Rather than scrambling for last-minute, low-value purchases, investing in proven tools to drive results across the organization with little ramp time just makes great financial sense. read more
Beyond UEBA: Elevating Insider Risk Management with Behavioral Intelligence
Insider risk management goes beyond UEBA expertise to evolve. Solutions must match up to the rise in insider security breaches. read more
Is IAM, SIEM, and DLP Enough to Combat Insider Risk?
Gaps in IAM, SIEM, and DLP tools leave insider risk undetected and unmitigated. Learn how to enhance your security by monitoring human behavior. read more
Insider Risk Management: Addressing the Human Side of Risk
Shifting to human-centric security, the human firewall helps prevent insider risk by managing behaviors at the individual level. read more
Why Understanding Human Behavior is the Future of Cybersecurity – Exclusive Interview
Elizabeth Harz, CEO of Veriato, shares her insights on the evolving landscape of insider risk management. Find out why understanding human behavior is crucial to preventing breaches and how Veriato’s solutions are leading the way. read more
Is Employee Monitoring Software Worth The Investment?
Key Takeaways: Employee monitoring software offers detailed insights into employee activities, enhancing productivity and bolstering data security. Choose the right software based on features, cost, ... read more
How To Choose The Right Employee Monitoring Software
Remote work is becoming increasingly common, and data breaches are a constant threat. The importance of employee monitoring software has never been more pronounced. For businesses looking to safeguard their digital ... read more
UEBA: Revolutionizing Security With Advanced Analytics
Key Takeaways: Behavior-Focused Security: UEBA revolutionizes cybersecurity by analyzing user behavior patterns, providing a dynamic approach to detecting anomalies and potential threats. Flexible and ... read more
Insider Threat Detection In Modern Enterprises
Key Takeaways: Detect Before It's Too Late: Insider threats are multifaceted, encompassing malicious actions, negligent behaviors, and external infiltrators, making comprehensive detection strategies ... read more
How to Better Manage Cybersecurity Risk With Human-Centric Approach
While technology is incredibly valuable in the cybersecurity landscape, understanding the habits of the people that work for an organization provides benefits well beyond cybersecurity. read more
A Surge in Quiet and Loud Quitters Presents New Threats
Investing in an engaged workforce isn’t just good for a company’s productivity, it’s also a constructive way of reducing insider risks and threats. By actively monitoring for signs of quiet and loud quitters, companies can spot signs earlier and get ahead of issues. read more
Work From Home, Quiet Quitting, and How Insider Risk Has Changed
One important risk mitigation strategy that organizations should consider is better communication and analytics. By spotting issues and resolving them quickly, companies can reduce the number of risks that become threats. read more
Focusing On Productivity Helps Reduce Insider Risk
When employees feel cared for, they are actually less likely to create risks for their organizations, and when organizations focus on productivity, they create a culture of trust. This virtuous cycle can help insider risk stakeholders succeed in this work from anywhere world. read more
Elizabeth Harz RSAC 2023 Interview
Watch Elizabeth Harz's interview with ISMG at this year's RSA Conference in San Francisco. read more
A More Insightful, Proactive Approach to Employee Monitoring
Companies need a more proactive approach to understanding their remote and hybrid workforce and working together with employees to increase productivity and keep companies and employees safe. read more
Bossware and the Future of Work
One positive change that many companies are making is to shift their thinking from “monitoring” to “analyzing.” With software that helps companies understand the productivity patterns of their workforce, the focus can be on the productivity itself and not as much on the monitoring of employees. read more
The Myths and Truths of Employee Monitoring
Early in the pandemic, searches related to “how to monitor employees working from home” increased by 1,705%. Without the oversight of managers in an office setting, many companies are concerned that their employees ... read more
When To be Suspicious About Work-From-Home Employees (or Not)
Good leaders understand what signs point to suspicious behavior, and which signs are simply a product of the new work-from-home norm. read more
Avoid These Employee Monitoring Blunders
Managers and executives need to avoid poor planning, bad communication and unreasonable expectations getting in the way of a successful employee monitoring implementation. read more
How to Rebrand ‘Bossware’ at Your Company
Monitoring has effects on employees that company executives should address to ensure a healthy work environment, increase productivity and reduce employee turnover. read more
The Future of Work Requires More Transparent Management
With many people working from home, companies need a better way to monitor productivity. It’s time to rethink employee monitoring to consider employee well-being. read more
How to Establish an Insider Risk Security Team
Learn how to establish an insider threat security team to mitigate risks and ensure the remote work environment is conducive to organizational security. read more
Awareness Earns ISO/IEC 27001:2013 Certification to Manage Information Securely
Awareness Technologies Inc, parent company of Veriato and Interguard, today announced that the organization has earned ISO/IEC 27001:2013 certification. read more
Are Your Employees Creating Risks For Your Organization While Working at Home?
Insider risk has changed considerably with the rise of remote work, and it’s important for companies to change, as well. read more
Insider Risk Looms the Manufacturing Industry: Tips to Mitigate
Manufacturing ranks among the top five industries with the highest reported insider breaches and privilege misuse. In Verizon's Data Breach Investigations Report, nearly 40% of the cybersecurity incidents in manufacturing traced to insiders, including partners and third-party vendors. The same report outlined 57% of database breaches to an insider within the organization. read more
3 Surprising Ways Ransom Attacks Could Destroy the 2022 Olympic Games
Though the level of fear of Covid 19 has diminished, there are other fears surrounding the 2022 Olympic games. Fears of telecom disruptions and ransomware attacks are founded, and the damage that could be caused has increased with the reliance on technology to broadcast the Games, which kicks off on February 4. read more
Combatting Insider Threats in Remote Learning Environments
Remote learning is now an inevitable reality for academic institutions. Learn more about combating insider risk while remote learning is on the rise. read more
Defending Against Social Engineering Attacks with Modern Insider Threat Management
Defending Against Social Engineering Attacks with Modern Insider Threat Management read more
Leveraging National Cybersecurity Awareness Month to Reduce Insider Threats
Increase your remote workers’ productivity with this innovative employee productivity solution. read more
Cybersecurity in Higher Education: Understanding the Threats & Adopting A Zero Trust Approach
Why colleges and universities are an attraction for cyber attacks read more
How to Build Your Employee Monitoring Posture to Combat Ransomware
Ransomware is a major threat faced by organizations and people around the world. It encrypts your files and holds them ransom. read more
What we can learn from the most alarming 2021 breaches so far
The escalation in cybersecurity breaches in 2020 has continued into 2021. Learn how to defend, prevent, detect, and respond to cyber attacks. read more
Picking the Right Comprehensive Threat Detection Solution
Navigating Cybersecurity Tool Fatigue and Picking the Right Comprehensive Threat Detection Solution read more
Expert advice on approaching HIPAA data security
Learn from top security experts about the concerns facing HIPAA data security in today’s digital world. read more
Insider Threats and the Dark Web increase Remote Work Risks
Threats related to remote continue to rise. Veriato’s AI-based, advanced threat mitigation solutions ensure your remote working environment is protected. read more
Employee Productivity Solution For Remote Workers
Increase your remote workers’ productivity with this innovative employee productivity solution. read more
How to Use Workplace Investigation Software
Learn how to use workplace investigation software to monitor your employees and protect your business. read more
Do’s and Don’ts of Using Software For Monitoring Computers
Make the most out of software for monitoring computers by following these simple do’s and don’ts. read more
Five Cybersecurity Priorities to focus on in 2021
The world may have changed, but cybersecurity is still a major battleground. Learn how to make 2021 a year of secure remote working. read more
How to Monitor User Activity
Learn how to monitor user activity on company-owned devices using monitoring software. read more
How Are Managers Remote Monitoring Computers for Remote Workers?
Learn how managers are remote monitoring computers for remote workers using innovative software. read more
Securing your businesses beyond the office perimeter
In a hybrid office environment, monitoring solutions with an increased emphasis on user activity and security events are useful. Read to learn more. read more
How Software Can Help With A Digital Workforce Transformation
Are you managing remote workers? The key to a successful digital workforce transformation is the right software. read more
Employee Monitoring For the Remote Workforce
Learn the ins and outs of employee monitoring for employees that are working remotely. read more
Managing Compliance and Security in a Remote World
As the digital enterprise became a reality, cyber attacks against data soar. Read on to see how to benefit your company, customers, and remote workers. read more
The Importance of User Behavior Analytics
Don’t underestimate the importance of user behavior analytics. Learn about the many uses and benefits of this data. read more
Employee PC Monitoring Software
Learn how to monitor your employees’ computer activity using Veriato PC monitoring software. read more
Easy Ways to Boost Employee Productivity Remotely
Take a look at some easy ways to boost employee productivity remotely. read more
Using AI to Detect & Prove HR Related Employee Violations
AI tools such as UEBA and UAM offers an enterprise a means to unobtrusively monitor employees while minimizing commercial disruption. read more
Bringing UEBA & Zero Trust Together Making Remote Work Safer
The use of UEBA (User & Entity Behavior Analytics) within a Zero Trust model is smart enough to handle the complex situations that remote working presents. read more
Track Employees’ Online Activity With Computer Monitoring Software
Use Veriato computer monitoring software to protect your business and see exactly what employees are doing at work. read more
Top Benefits of Using an Employee Time Tracking App
Learn about the benefits of using an employee time tracking app and how this benefits companies working remotely. read more
Your Ultimate Guide to Managing Productivity in a Remote Workplace
A distributed workforce is not without its challenges. You need a dynamic plan for cybersecurity and employee monitoring when working from home. read more
5 Cyber Threats That Won’t Disappear After The Pandemic
5 important cyber threats that businesses must be prepared to face after the pandemic, and the security strategies and tools that can help minimize impact. read more
Why Does Your Business Need Employee Time Tracking Software?
Can making the switch from manual timekeeping to employee time tracking software really influence the success of your company? read more
What is Corporate Espionage?
What is corporate espionage? Here’s what you need to know about this illegal business practice. read more
Can AI Predict Workplace Violence?
While the majority of the cybersecurity industry is focused on securing data, the growing convergence of digital and physical security remains unhinged. read more
Exploiting the Pandemic: Cyber Security Breaches in 2020
Exploiting the Viral Pandemic: Targeted Cyber Security Breaches in 2020 have Cost Privacy, Infrastructure, and the Lives of the Most Vulnerable in Society read more
What are the Benefits of Employee Time Tracking?
Use an employee time tracking system to track employee idle time, session duration, and project lifecycles, leading to improved productivity company-wide. read more
How to Prevent Industrial Espionage
Don’t fall victim to industrial espionage. Here are the steps you should take now to protect your company. read more
Managing Cyber Threats to Operational Technology
Managing Cyber Threats with an emphasis on the manufacturing and healthcare industry read more
How Can You Detect an Insider Threat?
Take a look at some of the ways you can identify, address, and prevent an insider threat from damaging your business. read more
Two-Years Later: The Current State of GDPR & its Impact on Businesses
The part that employee threats play in GDPR compliance. Two Year GDPR Anniversary Edition: Balancing compliance and employee monitoring. read more
Protect Your Business with Digital Forensics Software
Digital forensics software provides you a streamlined and accurate way to handle internal investigations and prevent cybercrime for your small business. read more
Are Workers Actually Working? Remote Work during Coronavirus
Are your employees actually working? Are they sitting at their desk when they should be? Find out more about how the pandemic is affecting remote workers. read more
Cyber Crime Investigation: Insider Threats
Is your company prepared? Here’s what you need to know about conducting a cyber crime investigation into insider threats. read more
Why Does Your Business Need Digital Forensic Tools?
Cybercriminals leave a trace just like real-world offenders. Read on to learn more about how digital forensics tools can keep your company protected. read more
Forensic Software – Getting the Proof You Need
If an employee needs investigating, consider using forensic software. It can provide the proof you need, without tipping off your staff. read more
Computer Forensic Tools – Providing The Evidence You Need
Computer forensic tools help make employee investigations more efficient. Save money and time by gathering complete indisputable evidence. read more
Cybersecurity Implications Of An Ongoing Pandemic
From a fully remote workforce, to cyber attackers, technology is playing a pivotal role in the way the coronavirus pandemic plays out. read more
Coronavirus: 10 Steps Employers Can Take to Maintain a Safe Workplace
Here are 10 steps employers need to take to keep your workplace safe in the face of a public health emergency. read more
Should you be worried about false negative insider threats?
Insider threats often go undetected. Trusted employees have better chances of getting away with the attack. read more
Monitoring a Mobile Workforce
Statistics show that even without an imminent threat from illnesses, companies would do well to prepare for the employees who work remotely. read more
The Evolution of Digital Forensics
Digital investigations & forensics methods have become critical to solving workplace investigation cases involving employee data theft and insider threat. read more
Workforce Management Software
Without workforce management software, any large company’s human resources department is likely to be stressed and overworked. read more
What is Next Generation Threat Hunting?
With cybercrime at an all-time high and criminal attack techniques growing in sophistication, the losses associated are record-breaking. read more
Advanced Solutions for Data Theft and Fraud Detection
The threats from data theft and fraud will continue to be a significant concern for all corporate entities in 2020. read more
Reducing Cyber Risk With AI and User Behavior Analytics
See, understand, and have reliable records of what users are doing with corporate assets. Collect valuable insights when reducing cybersecurity risks . read more
Cyber Security Trends in the Energy Sector
Cybersecurity trends in the energy sector. read more
Five Reasons Why “Never” Being Breached May Not Be A Good sign
Countless companies have found themselves in the headlines after being breached over the last decade, there are also many companies we never hear about. read more
How to Choose a Computer Tracker for Employee Monitoring
Selecting a computer tracker for employee monitoring can feel like a real challenge. What should you look for in a monitoring software. read more
Why Use A Free Computer Monitoring Software?
Free computer monitoring software can help managers track productivity, protect sensitive data, and provide employees with better feedback. read more
Employee Tracking: Uses and Benefits
Many companies feel the need to track employees to oversee productivity, but the benefits of employee tracking software extend beyond these core needs. read more
How to Use Web Monitoring to Prevent Employee Fraud
Find out why many employers use web monitoring software to prevent employee fraud and protect their business. read more
How Cyber Attackers Hide Their Tracks After Committing Digital Fraud?
Attackers go above and beyond to evade alerting capabilities and make it look like they were never there. read more
5 Tips to Choose the Best Internet Monitoring Software
Overseeing employee’s daily activities is impossible. Monitoring software may help ensure that productivity doesn’t dwindle and company business remains. read more
5 Must Have Features in Employee Tracking Software
Employees are both your biggest asset and biggest risk. With employee tracking software, the risks can be dramatically reduced . read more
What to Look for in an Activity Monitor for Windows
When searching for an activity monitor for Windows, there are certain features that should be considered. What are the most important features to look for? read more
7 Reasons You Should Be Using Employee Monitoring Software
7 reasons why your company should be using employee monitoring software. Without employee monitoring, your business is at risk read more
The Secret to Boosting Employee Productivity
Unproductive workers could affect a company’s financial outlook and perhaps even sour client relationships. read more
How to choose the Best Productivity Tracker in 2020
By choosing the best employee productivity tracker, you help your business’s efficiency and profitability. read more
User Behavior Analytics: Preventing Security Threats
User behavior analytics helps employers stay ahead. Get alerted when staff perform actions outside of their normal role. read more
How to Prevent Employee Fraud with Stealth Monitoring
Workplace crimes like financial theft and fraud can leave a company open to litigation and serious financial losses. read more
What is the Best Employee Time Tracking Software?
Ensuring that employees keep their personal time off the clock might require that companies keep a close eye on computer data via time tracking software. read more
6 Reasons Computer Monitoring can improve Employee Productivity
Find out how using computer monitoring software can drastically improve employee productivity. read more
Cybersecurity Trends in Agriculture
The agriculture sector is a staple of critical global infrastructure. We need food to survive, a loss of these assets could be detrimental. read more
Cybersecurity 101 For Entrepreneurs And Start-Ups
No matter how small in size or how new on the startup scene, these growing companies often face the same cyber risks that well-established companies face. read more
Key tips to finish your 2019 cyber year strong and prepare for 2020
Forbes released its list of 2019 cybersecurity projections. Central themes included predictions on the growth of nations involved in cyber warfare & more. read more
Disturbing Cybersecurity Trends In Aviation
Aviation is a critical infrastructure comprised of a web of public and private organizations relying on millions of assets to move people and cargo around read more
Five Ways Cyber-Attackers Are Using AI to Their Advantage
Industries are raving about all of the ways that artificial intelligence can help transform the world into a more efficient and productive environment. read more
Five Challenges Companies Face When Attempting to Embrace AI
Artificial intelligence is one of the biggest buzzwords of the year. It seems to be a much-needed answer to woes across various industries & challenges. read more
When Employees Waste Time, and What to Do About It
Employees spend just 40% of their workday on primary tasks. So how can an organization find out what employees are doing when they are on the clock? read more
Five Ways AI is Cutting Costs in Start-Ups and Small Businesses
Companies of various sizes have embraced the concept of the lean startup. read more
A Quick Guide To Visibility And Smarter Monitoring
Data breaches happen and can take months to discover. Companies with the right monitoring technology have the ability to detect & respond to these threats. read more
Cybersecurity Trends In The Government Sector
Government agencies and their assets are subject to the same cyber threats that private sector companies face. read more
Major Breaches Highlighting Importance of Visibility in the Workplace
Rapidly detecting an incident can be the difference between the survival or closure of a company after a cybersecurity breach. read more
The Rise of Predictive Threat Detection
Advancements within the cyber security space are driving a critical shift from reactive threat detection to modern predictive threat detection. read more
Five Things You Should Know About Enterprise Visibility
Data breaches happen daily, many of which go undetected for months and even years. read more
Are Your Employees Watching Netflix at Work?
Workplace productivity is directly related to company profitability. Employers are seeking ways to cut waste, i.e activities that eat into productivity. read more
Cyber Security Trends in the Tech Industry
The tech industry is one of the most swiftly evolving areas of business today. read more
The Rise of Ransomware as a Service (RaaS)
Ransomware is a form of cyber - attack in which criminals block access to prized digital possessions or resources and demand payment for their release. read more
Four Misconceptions About Ransomware Addressed
Ransomware has been a hot topic within the cyber security industry and is cyber-attack method with an attractive return on investment. read more
Guide to Preventing, Detecting and Responding to Ransomware Attacks
Despite a small decline in the total volume of ransomware attacks, assailants are leveraging the attack method as a targeted way to extort enterprises. read more
Notable Ransomware Attacks from 2019 and Lessons Learned
Examples of successful ransomware attacks and lessons we can learn from each. read more
What is Ransomware?
Since the first documented ransomware attack occurred, the attack method has increasingly become a threat to organizations and individual consumers. read more
Is Cultural Transformation the Secret to Productivity?
Employee Monitoring Software, Employee Productivity, veriato, veriato employee monitoring software read more
Employee Investigations 101
An employee investigation is a process for gathering, analyzing, and reporting on evidence regarding an Insider Threat within an organization. read more
Five Common Insider Threat Profiles
Insider Threats come in many different shapes and forms and can be a frustrating problem to diagnose. read more
7 Ways to Make your Workforce More Productive
The US Department of Labor states that most people work an average of eight hours a day, but the question is, how many of those hours are productive? read more
Cyber Security Trends in Healthcare
A significant portion of breaches reported in the last year impacted the healthcare industry, and it was costly read more
A Quick Guide to Preventing, Detecting & Responding to Insider Threats
The key to addressing inevitable Insider Threats within organizations is to have a robust strategy to prevent, detect, and respond to such incidents. read more
Five Concerning Breaches That Started With an Insider Threat
Behind every breach is a human or entity orchestrating an attack to make it happen. read more
Insider Threat Detection Software to Increase Employee Productivity
Imagine that for every 100 employees you’ve hired, 70 of them are underperforming and disconnected from their work. read more
What is User and Entity Behavior Analytics and why does it matter?
The fundamental operating principle of UEBA is to create a picture of what normal user and organizational behavior looks like. read more
What Is DLP. Why Does It Matter. What Is Your Strategy Missing?
Once upon a time, protecting critical data assets meant keeping printed confidential information in locked boxes labeled top secret. read more
Dark Web Recruitment of Employees Puts Organizations at Risk
The idea of your employees being solicited on the Dark Web isn’t a hypothetical; it’s real, it’s tempting, and it’s lucrative. read more
What You Should Know About Ransomware in 2019
It’s estimated that Ransomware costs will climb to roughly $11.5 billion in 2019, according to CSO Online. read more
Five ways AI is being used in the cybersecurity industry
Businesses no longer have to spend hours sifting through financial records to detect fraud or manually investigating system logs during a cyber-attack. read more
What Is an Insider Threat and the 5 Things You Should Know?
According to a 2018 Ponemon Institute report, of those surveyed, ove 3k known insider threat incidents were reported with an average cost of about $238k. read more
Bad Password Management Puts Organizations at Risk
Ponemon’s State of Password and Authentication Security Behaviors Report highlights how inappropriate use of privileged password can give insiders access. read more
Apple Employee Steals Thousands of Self-Driving Car Files
No greater tech is at the forefront of cutting-edge technology than the self-driving car. read more
Why Data Breaches are caused by Employee Negligence
Every company wants to avoid a data breach. Most efforts are placed on protecting the environment from external threats attempting to get in. read more
Most Crime is Perpetrated by Employees Already Inside Companies
The introspective look at the UK’s £1.2 billion in 2018 fraud cases by KPMG demonstrates the need to be mindful of insiders. read more
Serious About Insider Threats? Start Paying Attention to the Dark Web
Insiders keen on making money from the valuable data your organization holds need a TOR browser to connect with buyers, hackers, and everyone else. read more
How to Detect Employee Fraud – Malicious Insider Protection
These are four tools & practices you can adopt to detect employee fraud should it happen in your organization & keep you protected from malicious insiders. read more
BASF Employees Caught Stealing Trade Secrets for Millions
One of the most valuable data sets any manufacturing company has is its intellectual property, proprietary processes, and product roadmaps. read more
Ex-UBS Employee Suspected of Data Theft Becomes a Fugitive
If it was your organization, you’d like to know based on logged user activity data from the application hosting the data stolen, right.? read more
Fight Timecard Fraud and Wage Theft with Employee Monitoring
Timecard fraud is more colloquially known as “lowered productivity,” as well as “employee wage theft” and it could be hurting your bottom line. read more
Who to Consider an Insider Threat in Your Organization
With 53 % of organizations experiencing at least one insider attack within the last 12 months, it’s imperative to understand who could be an insider. read more
How to Conduct a Workplace Investigation
Workplace investigations can be extremely tense. Here’s a step-by-step guide to conducting a timely, & thorough workplace investigation. read more
How to Maintain Data Security When Employees Work Remotely
How can you allow your employees to work remotely and still maintain security? Luckily there are many steps you can take to ensure data security. read more
How to Conduct an Endpoint Network Security Audit
An endpoint security audit is an excellent way to ensure your network is protected. Learn how to conduct one for your network. read more
Cyber Security Budget Trends for Businesses in 2019
Here are a few cyber security trends to adopt in 2019 that will keep your organization’s information as safe as possible. read more
What is User and Entity Behavior Analytics?
UEBA sets baselines for human activity and also for the activity of the machines connected to the network. read more
Election Interference Attacks More than Voting Machines
When election interference is discussed, you probably think of hacked voting machines. But interference can come in many other forms. read more
What you should do after a spear phishing attack
Spear phishing is very common and the likelihood it happens to someone in your organization is high. If there is an attack, here is what you need to do. read more
2 Big Steps to Keep Electronic Health Records Secure
The fear of stolen PHI and its consequences is so strong that many healthcare organizations have yet to fully adopt digitization. read more
Why Zero Trust Is Not As Bad As It Sounds
Zero Trust means organizations never implicitly trust anyone with their sensitive data. read more
How to Create Incident Response Plan Steps for Data Breaches
By following these steps to create your incident response plan you’ll minimize damage to your network. read more
Machine Learning Protects Employee Privacy & Data Security
Employee monitoring software leveraging machine learning prioritizes both employee privacy and data security by tracking activity, not people. read more
How to Protect Against a Ransomware Attack
Ransomware is changing so are network security offerings. Here are a few things you need to know to protect your business against a ransomware attack. read more
The CA Consumer Privacy Act | What Businesses Need to Know
Even if your business is not located in California, you may be liable under the CA Consumer Privacy Act - so here’s everything you need to know. read more
How Employee Monitoring Keeps Clinical Trial Data Secure
Many organizations rely on 3rd party services to handle their data. Increasing the number of people who can access data increases the risk of insiders. read more
Cyber Incident Reporting Compliance for Federal Contractors
Federal regulations require federal contractors to report a cyber incident “rapidly” – defined as within 72 hours of discovery of the breach. read more
Data Security Considerations for Your Work From Home Policy
Work from home policies have soared in popularity. Take these data security considerations into account when creating your work from home policy. read more
The Severity of Cyber security Threats
Cyber security threats are being realized by vulnerable organizations large and small. read more
Best practices for securing your data when terminating an employee
Secure your data when terminating an employee. Make sure the employee is the only thing you lose by securing your data when terminating an employee. read more
Employee Monitoring Ethics | Ethically Monitoring Employees
Is employee monitoring ethical? Organizations have a right to protect their data and a responsibility to their employees and clients. read more
The Benefits of Starting A User Activity Monitoring System
If you’re on the fence about starting a user activity monitoring system (UAM) across devices , you’re probably wondering if it’s worth the investment. read more
GDPR Mandates Immediate Data Breach Reporting
GDPR mandates that notification must be given when a breach is likely to “result in a risk for the rights and freedoms of individuals”. read more
General Data Protection Regulation Compliance Objectives
The EU General Data Protection Regulation (GDPR) is the most significant regulation regarding data privacy in over 20 years. read more
The Growth of AI and Employee Monitoring In the Workplace
Recently the Economist published two articles that discussed the increasing us of AI and employee monitoring in the workplace. read more
Internet of Things security practices for your business
The Internet of Things (IoT), or internet-enabled devices that collect and act upon data, is becoming more popular with ever-increasing applications. read more
3 ways cyber security is changing business operations
As cyber security receives more consideration, business operations are changing to prioritize data safety. read more
4 reasons to increase hospital cyber security budget
Health organizations are allocating less than half of what other industries budget for Information Security. read more
Technical safeguards for HIPAA at the administrative level.
Learn from experts how establishing HIPAA technical safeguards at the administrative level can help with staying HIPAA compliant. read more
Security concerns and solutions for staying HIPAA compliant
While HIPAA itself isn’t broken out into separate objectives for each stakeholder, stakeholders each have different needs around adhering to HIPAA. read more
Defense Against Enemies, Foreign and Domestic
The inclusion of defense against domestic threats points to our Civil War and the desire to keep intact something that is fragile and worth defending. read more
Insider Threats are a Risk to Your Data—Here’s How to Stop Them
Most companies have already hunkered down to prevent hackers from stealing proprietary data. Security teams have certainly installed powerful firewalls. read more
U.S. Elevates Cyber Command to Combatant Status
Whether with national security or your enterprise security, cyber security should not be marginalized on the sidelines. read more
Additional Insight into Quantifying Insider Risk
Never before have there been so many platforms that let a growing number of people touch, manipulate, download, and share sensitive data. read more
Why Trust is not Enough
Why high risk positions need to be monitored closely to help combat insider threats & how User Behavior Analytics & User Activity Monitoring can help. read more
How to Prevent Departing Employees from Pocketing Your IP
When George started his current position 10 years ago, he brought hundreds of business notes that he added to his employee’s customer management software. read more
To cloud, or not to cloud. That is the question.
Thinking about storing sensitive information in the cloud? Be sure of the security of that data you would be storing on your own infrastructure. read more
Malware Evading Some Antivirus Using Invalid Certificates?
Many antivirus and endpoint security technologies fight two-sided battle. On the one hand, they must block malware threats from executing on the system. read more
Don’t Be Held Hostage By Ransomware
Ransomware, a type of malware that encrypts your critical files until money is paid, continues to wreak havoc on organizations worldwide. read more
Quantifying the risk of an insider data leak
One of the challenges associated with combating the threat of insider data leaks stems from a lack of understanding of the risk in the perimeter. read more
4 Steps to Decrease the Risk of Malicious Insider Activity
Improve your organizational ability to detect insider threats before they become insider attacks and react quickly read more
3 Steps To Protect Your Data From Leaving With A Departing Insider
What is the High Risk Exit Period? It’s the period of time between when an insider decides to leave the organization and the day they actually do leave. read more
The Widespread Risk of Insider Threats
There is a great infographic by Deloitte on the topic of insider threats. They've done a wonderful job packing a great deal of information into. read more
Best Practices for Mitigating Insider Threats
Here we highlight 5 of the 19 practices that we believe can have a significant positive impact on your ability to secure against the insider threat. read more
5 employee cyber security training questions you need to ask
Chances are your organization already addresses cyber security training in new employee onboarding. read more
The Rise of User Behavior Analytics
Gartner published the Market Guide for User Behavior Analytics. The analysts did a great job defining what had beforehand been a largely undefined market. read more
Is Employee Monitoring Legal?
As the number of insider theft, fraud, or lower productivity continues to rise, more companies recognize the need for an employee monitoring program. read more
Read this. Pick yourself up off the floor. Then Trust, but Verify.
I work for a company that makes behavioral analytics software for insider threat detection and user activity monitoring software, read more
Attack the problem before the problem attacks you
In our most recent post we identified that only a small number (21%) of organizations are continuously monitoring the behavior of their users. read more
One million six hundred ninety-one thousand reasons to look inside
62% of security professionals who took part in the survey believe insider attacks have become more frequent in the last 12 months. read more
The data says it’s the data
63% of survey respondents are most concerned with data leaks stemming from insider attacks. read more
The disgruntled employee insider threat
Computerworld UK has a great article out on the insider data breach at Morrisons supermarkets in the United Kingdom. read more
A Not Exactly Up-Lyfting Incident
If you haven't seen the news about Lyft and its former COO, check out the great write-up by Ryan Lawler over at TechCrunch.com. read more
The barbarians are through the gate.
Insider threats are a big topic - in the news and here at Veriato. read more
Veriato, formerly known as SpectorSoft FAQ
Wondering how SpectorSoft changing to Veriato may affect you? See below for answers to questions that you may have. read more
What’s in a name? And why change it?
We’ve changed our name to Veriato. So what? Companies change names all the time. Or they change a logo, or their brand color. read more
Are we counting on a Maginot Line?
A whole lot of time and money gets spent preventing acts or behaviors from happening. read more
Can you keep a secret?
According to USPTO.gov, trade secrets consist of info that can include formulas, compilations, programs, devices, methods, techniques or processes. read more
Could You Have Seen It Coming?
Anticipating potential employee issues, and having a plan to detect them is a key part of a comprehensive insider risk/insider threat mitigation plan. read more
Fact: Employees Leave Your Company
Whether it's a 'the door is always open' farewell, or a 'don't let the door hit you' see ya, there are steps to take to protect your company's interests. read more
Dealing With Insider Risk Starts Before They’re An Insider
Does your company have a 'one size fits all' approach to screening perspective hires? read more