Workplace productivity is directly related to company profitability. Employers are seeking more and more ways to cut waste – including wasteful activities that eat into productivity. Many companies would immediately agree that playing video games, spending excessive time on social media and streaming videos are blatant violations of workplace acceptable use policies.
Now consider that technologies are being created to help employees look productive while actually watching movies and television shows.
One workplace tool to enhance productivity is Google Hangouts which provides video conferencing, chat and voice calls conveniently within Chrome. However, there is another tool targeting would-be slackers to appear as if on a conference call while actually catching up on Netflix videos.
It’s a Google Chrome extension called Netflix Hangouts and appears to the unwitting eye as Google Hangouts with four active video panes – three with fake webcam streams and one where the user can binge-watch their shows and potentially evade passers-by who don’t want to disturb a co-worker or subordinate busy on a 5-way video conference.
The extension is marketed with screenshots such as this:
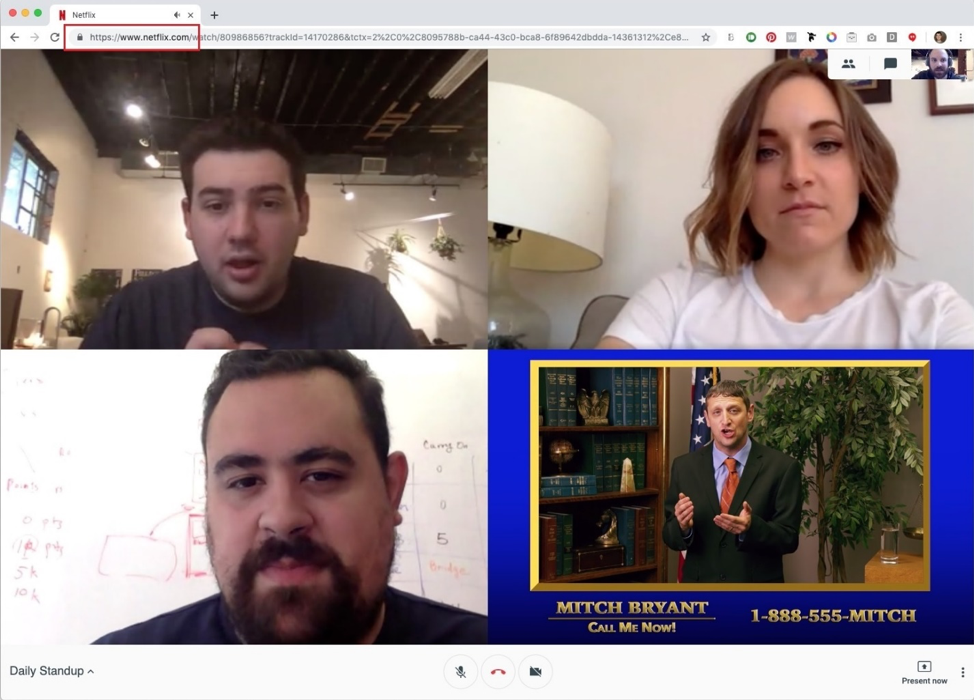
However, the browser continues to be connected directly to and stream from Netflix.com. The extension simply modifies the Netflix page to appear as Google Hangouts in video conferencing mode.
The Veriato Cerebral Employee Monitoring Platform can not only alert on any access of Netflix.com URLs but it can also be used to block access if the organization needs to limit access to non-work-related websites on company assets.
If you do not already have a Veriato Event Alert for Netflix.com access, you can create one using the “Alert – Events” interface under the “Alerts & Policies” menu in the Veriato Management Console.
For blocking access, add the “Netflix.com” domain to any recording policies using the “Block” –> “Websites Visited” feature.
You may also want to review how much active time is spent on this and similar sites by reviewing the Active, Focus and Total times for websites in the Veriato Management Console by specific users or in the Data Explorer under “Activity Types” -> Web Site Events. This can indicate whether that activity was merely an anomaly or if serious time is being spent on amusement.
Recently, the New York Times reported that 37 percent of employees admitted to watching Netflix at work. That can be a huge chunk out of profitability.

Insider Risk Management Guide to Behavioral Visibility
Discover how modern Insider Risk Management leverages behavioral visibility, sentiment analysis, and AI-driven risk scoring to strengthen security, compliance, and workforce resilience.